RANSOM_MILICRY.A
Windows


Threat Type: Trojan
Destructiveness: No
Encrypted: Yes
In the wild: Yes
OVERVIEW
This ransomware uses a free photo upload service as its C&C server. This way, it is able to mask its C&C routines.
To get a one-glance comprehensive view of the behavior of this Trojan, refer to the Threat Diagram shown below.
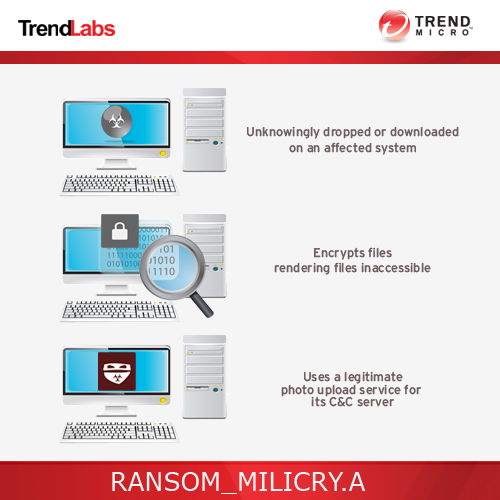
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
TECHNICAL DETAILS
Arrival Details
This Trojan arrives on a system as a file dropped by other malware or as a file downloaded unknowingly by users when visiting malicious sites.
Installation
This Trojan drops a copy of itself in the following folders using different file names:
- %User Temp%\{random filename}.exe
(Note: %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
It creates the following folders:
- %Desktop%\old_shortcut-Transfers here all the files/folders/shortcuts currently in your desktop that haven't been encrypted.
(Note: %Desktop% is the desktop folder, where it usually is C:\Documents and Settings\{user name}\Desktop in Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\Desktop in Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Other System Modifications
This Trojan adds the following registry keys:
HKEY_CURRENT_USER\Software\{random filename}
HKLM\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
CtlGuid
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
ServiceCtlGuid
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WLanDiagCtlGuid
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
DiagL2SecCtlGuid
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WDiagCoreCtlGuid
It adds the following registry entries:
HKEY_CURRENT_USER\Software\{random filename}
{random file name 1} = "{hex values}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
CtlGuid
Guid = "{GUID}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
ServiceCtlGuid
Guid = "{GUID}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
ServiceCtlGuid
BitNames = "DOT11_AUTOCONF DOT11_AUTOCONF_CLIENT DOT11_AUTOCONF_UI DOT11_FATMSM DOT11_COMMON DOT11_WLANGPA DOT11_CLASS_COINSTALLER"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WLanDiagCtlGuid
Guid = "{GUID}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WLanDiagCtlGuid
BitNames = "WLANHC_AUTOCONFIG WLANHC_RNWFMSM WLANHC_FATMSM WLANHC_DLLMAIN WLANHC_TEST"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
DiagL2SecCtlGuid
Guid = "{GUID}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
DiagL2SecCtlGuid
BitNames = "SECHC_LOG_FLAG_ASSERT SECHC_LOG_FLAG_INIT SECHC_LOG_FLAG_DIAG SECHC_LOG_FLAG_ONEX_DIAG SECHC_LOG_FLAG_REPAIR SECHC_LOG_FLAG_STATE SECHC_LOG_FLAG_EXT SECHC_LOG_FLAG_EVENT_LOG SECHC_LOG_FLAG_FUNCTION SECHC_LOG_FLAG_MEMORY SECHC_LOG_FLAG_LOCKS"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WDiagCoreCtlGuid
Guid = "{GUID}"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing\
WDiagCoreCtlGuid
BitNames = "WD_LOG_FLAG_INIT WD_LOG_FLAG_RPC WD_LOG_FLAG_EVENT WD_LOG_FLAG_INTERFACE WD_LOG_FLAG_CONNECTION WD_LOG_FLAG_CONTROL WD_LOG_FLAG_LOCKS WD_LOG_FLAG_MEMORY WD_LOG_FLAG_REFERENCES WD_LOG_FLAG_FUNCTION_TRACE WD_LOG_FLAG_ASSERT"
It modifies the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Settings\
ZoneMap
ProxyBypass= = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Settings\
ZoneMap
IntranetName = "1"
HKEY_CURRENT_USER\Software\Microsoft\
Windows\CurrentVersion\Internet Settings\
ZoneMap
UNCAsIntranet = "1"
HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\
Windows NT\CurrentVersion\Tracing
LogSessionName = "stdout"
Dropping Routine
This Trojan drops the following files:
- %User Startup%\{random file name 1}.lnk-links to the dropped malware copy
- %User Startup%\{random file name 2}.lnk-links to the ransomnote
- %User Temp%\{random file name 3}.html-serves as ransomnote
- C:\0.tmp
- C:\1.tmp
- D:\2.tmp
- D:\3.tmp
(Note: %User Startup% is the current user's Startup folder, which is usually C:\Documents and Settings\{user}\Start Menu\Programs\Startup on Windows 2000 and XP, and C:\Documents and Settings\{User name}\Start Menu\Programs\Startup on Windows Vista, 7, and 8.. %User Temp% is the user's temporary folder, where it usually is C:\Documents and Settings\{user name}\Local Settings\Temp on Windows 2000, Windows Server 2003, and Windows XP (32- and 64-bit); C:\Users\{user name}\AppData\Local\Temp on Windows Vista (32- and 64-bit), Windows 7 (32- and 64-bit), Windows 8 (32- and 64-bit), Windows 8.1 (32- and 64-bit), Windows Server 2008, and Windows Server 2012.)
Other Details
This Trojan encrypts files with the following extensions:
- .dat
- .mx0
- .cd
- .pdb
- .xqx
- .old
- .cnt
- .rtp
- .qss
- .qst
- .fx0
- .fx1
- .ipg
- .ert
- .pic
- .img
- .cur
- .fxr
- .slk
- .m4u
- .mpe
- .mov
- .wmv
- .mpg
- .vob
- .mpeg
- .3g2
- .m4v
- .avi
- .mp4
- .flv
- .mkv
- .3gp
- .asf
- .m3u
- .m3u8
- .wav
- .mp3
- .m4a
- .m
- .rm
- .flac
- .mp2
- .mpa
- .aac
- .wma
- .djv
- .djvu
- .jpeg
- .jpg
- .bmp
- .png
- .jp2
- .lz
- .rz
- .zipx
- .gz
- .bz2
- .s7z
- .tar
- .7z
- .tgz
- .rar
- .zip
- .arc
- .paq
- .bak
- .set
- .back
- .std
- .vmx
- .vmdk
- .vdi
- .qcow
- .ini
- .accd
- .db
- .sqli
- .sdf
- .mdf
- .myd
- .frm
- .odb
- .myi
- .dbf
- .indb
- .mdb
- .ibd
- .sql
- .cgn
- .dcr
- .fpx
- .pcx
- .rif
- .tga
- .wpg
- .wi
- .wmf
- .tif
- .xcf
- .tiff
- .xpm
- .nef
- .orf
- .ra
- .bay
- .pcd
- .dng
- .ptx
- .r3d
- .raf
- .rw2
- .rwl
- .kdc
- .yuv
- .sr2
- .srf
- .dip
- .x3f
- .mef
- .raw
- .log
- .odg
- .uop
- .potx
- .potm
- .pptx
- .rss
- .pptm
- .aaf
- .xla
- .sxd
- .pot
- .eps
- .as3
- .pns
- .wpd
- .wps
- .msg
- .pps
- .xlam
- .xll
- .ost
- .sti
- .sxi
- .otp
- .odp
- .wks
- .vcf
- .xltx
- .xltm
- .xlsx
- .xlsm
- .xlsb
- .cntk
- .xlw
- .xlt
- .xlm
- .xlc
- .dif
- .sxc
- .vsd
- .ots
- .prn
- .ods
- .hwp
- .dotm
- .dotx
- .docm
- .docx
- .dot
- .cal
- .shw
- .sldm
- .txt
- .csv
- .mac
- .met
- .wk3
- .wk4
- .uot
- .rtf
- .sldx
- .xls
- .ppt
- .stw
- .sxw
- .dtd
- .eml
- .ott
- .odt
- .doc
- .odm
- .ppsm
- .xlr
- .odc
- .xlk
- .ppsx
- .obi
- .ppam
- .text
- .docb
- .wb2
- .mda
- .wk1
- .sxm
- .otg
- .oab
- .cmd
- .bat
- .h
- .asx
- .lua
- .pl
- .as
- .hpp
- .clas
- .js
- .fla
- .py
- .rb
- .jsp
- .cs
- .c
- .jar
- .java
- .asp
- .vb
- .vbs
- .asm
- .pas
- .cpp
- .xml
- .php
- .plb
- .asc
- .lay6
- .pp4
- .pp5
- .ppf
- .pat
- .sct
- .ms11
- .lay
- .iff
- .ldf
- .tbk
- .swf
- .brd
- .css
- .dxf
- .dds
- .efx
- .sch
- .dch
- .ses
- .mml
- .fon
- .gif
- .psd
- .html
- .ico
- .ipe
- .dwg
- .jng
- .cdr
- .aep
- .aepx
- .123
- .prel
- .prpr
- .aet
- .fim
- .pfb
- .ppj
- .indd
- .mhtm
- .cmx
- .cpt
- .csl
- .indl
- .dsf
- .ds4
- .drw
- .indt
- .pdd
- .per
- .lcd
- .pct
- .prf
- .pst
- .inx
- .plt
- .idml
- .pmd
- .psp
- .ttf
- .3dm
- .ai
- .3ds
- .ps
- .cpx
- .str
- .cgm
- .clk
- .cdx
- .xhtm
- .cdt
- .fmv
- .aes
- .gem
- .max
- .svg
- .mid
- .iif
- .nd
- .2017
- .tt20
- .qsm
- .2015
- .2014
- .2013
- .aif
- .qbw
- .qbb
- .qbm
- .ptb
- .qbi
- .qbr
- .2012
- .des
- .v30
- .qbo
- .stc
- .lgb
- .qwc
- .qbp
- .qba
- .tlg
- .qbx
- .qby
- .1pa
- .ach
- .qpd
- .gdb
- .tax
- .qif
- .t14
- .qdf
- .ofx
- .qfx
- .t13
- .ebc
- .ebq
- .2016
- .tax2
- .mye
- .myox
- .ets
- .tt14
- .epb
- .500
- .txf
- .t15
- .t11
- .gpc
- .qtx
- .itf
- .tt13
- .t10
- .qsd
- .iban
- .ofc
- .bc9
- .mny
- .13t
- .qxf
- .amj
- .m14
- ._vc
- .tbp
- .qbk
- .aci
- .npc
- .qbmb
- .sba
- .cfp
- .nv2
- .tfx
- .n43
- .let
- .tt12
- .210
- .dac
- .slp
- .qb20
- .saj
- .zdb
- .tt15
- .ssg
- .t09
- .epa
- .qch
- .pd6
- .rdy
- .sic
- .ta1
- .lmr
- .pr5
- .op
- .sdy
- .brw
- .vnd
- .esv
- .kd3
- .vmb
- .qph
- .t08
- .qel
- .m12
- .pvc
- .q43
- .etq
- .u12
- .hsr
- .ati
- .t00
- .mmw
- .bd2
- .ac2
- .qpb
- .tt11
- .zix
- .ec8
- .nv
- .lid
- .qmtf
- .hif
- .lld
- .quic
- .mbsb
- .nl2
- .qml
- .wac
- .cf8
- .vbpf
- .m10
- .qix
- .t04
- .qpg
- .quo
- .ptdb
- .gto
- .pr0
- .vdf
- .q01
- .fcr
- .gnc
- .ldc
- .t05
- .t06
- .tom
- .tt10
- .qb1
- .t01
- .rpf
- .t02
- .tax1
- .1pe
- .skg
- .pls
- .t03
- .xaa
- .dgc
- .mnp
- .qdt
- .mn8
- .ptk
- .t07
- .chg
- .#vc
- .qfi
- .acc
- .m11
- .kb7
- .q09
- .esk
- .09i
- .cpw
- .sbf
- .mql
- .dxi
- .kmo
- .md
- .u11
- .oet
- .ta8
- .efs
- .h12
- .mne
- .ebd
- .fef
- .qpi
- .mn5
- .exp
- .m16
- .09t
- .00c
- .qmt
- .cfdi
- .u10
- .s12
- .qme
- .int?
- .cf9
- .ta5
- .u08
- .mmb
- .qnx
- .q07
- .tb2
- .say
- .ab4
- .pma
- .defx
- .tkr
- .q06
- .tpl
- .ta2
- .qob
- .m15
- .fca
- .eqb
- .q00
- .mn4
- .lhr
- .t99
- .mn9
- .qem
- .scd
- .mwi
- .mrq
- .q98
- .i2b
- .mn6
- .q08
- .kmy
- .bk2
- .stm
- .mn1
- .bc8
- .pfd
- .bgt
- .hts
- .tax0
- .cb
- .resx
- .mn7
- .08i
- .mn3
- .ch
- .meta
- .07i
- .rcs
- .dtl
- .ta9
- .mem
- .seam
- .btif
- .11t
- .efsl
- .$ac
- .emp
- .imp
- .fxw
- .sbc
- .bpw
- .mlb
- .10t
- .fa1
- .saf
- .trm
- .fa2
- .pr2
- .xeq
- .sbd
- .fcpa
- .ta6
- .tdr
- .acm
- .lin
- .dsb
- .vyp
- .emd
- .pr1
- .mn2
- .bpf
- .mws
- .h11
- .pr3
- .gsb
- .mlc
- .nni
- .cus
- .ldr
- .ta4
- .inv
- .omf
- .reb
- .qdfx
- .pg
- .coa
- .rec
- .rda
- .ffd
- .ml2
- .ddd
- .ess
- .qbmd
- .afm
- .d07
- .vyr
- .acr
- .dtau
- .ml9
- .bd3
- .pcif
- .cat
- .h10
- .ent
- .fyc
- .p08
- .jsd
- .zka
- .hbk
- .mone
- .pr4
- .qw5
- .cdf
- .gfi
- .cht
- .por
- .qbz
- .ens
- .3pe
- .pxa
- .intu
- .trn
- .3me
- .07g
- .jsda
- .2011
- .fcpr
- .qwmo
- .t12
- .pfx
- .p7b
- .der
- .nap
- .p12
- .p7c
- .crt
- .csr
- .pem
- .gpg
- .key
It renames encrypted files using the following names:
- {filename of encrypted files}.cry
It does the following:
- Deletes shadow volume:
- "%System%\vssadmin.exe" delete shadows /all /quiet
- Sends the following data to the server :
- System information
- Files encrypted
- It sends the gathered data to the following URL:
- http://{BLOCKED}r.com/a/RkI0O
- It sends the gathered data to the following URL if it fails to connect to the first URL:
- http://{BLOCKED}in.org/submit
- It will not encrypt if the system's language is any of the following:
- Kazak
- Russian
- Ukrainian
- Uzbek
- Sakha
- Belarusian
NOTES:
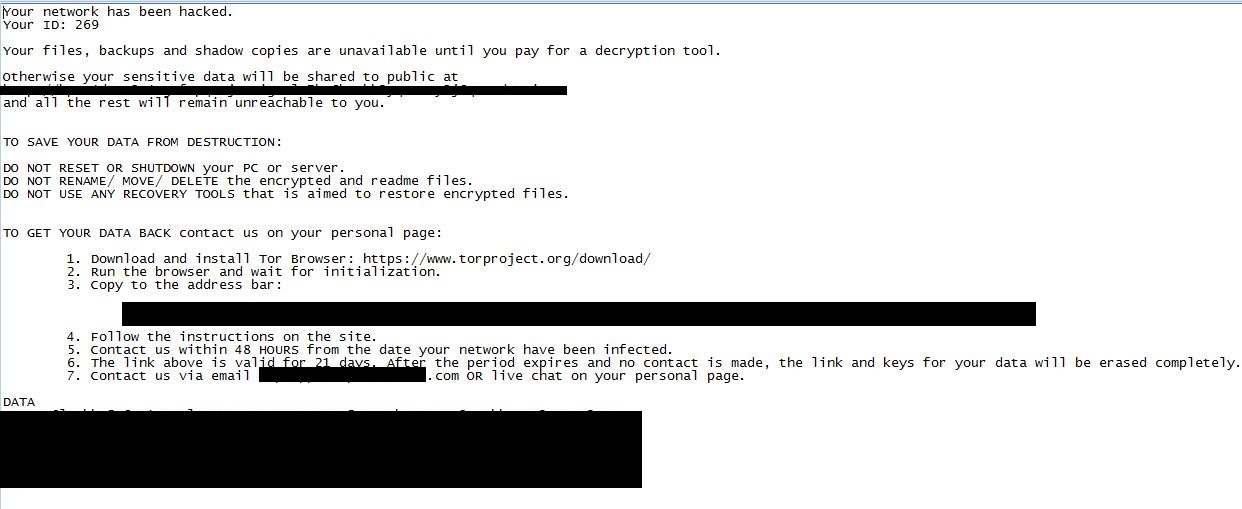
This ransomware drops the following ransomnote:
It displays the following in the given personal homepage:
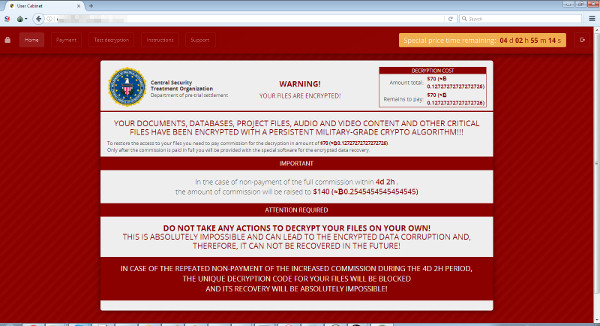
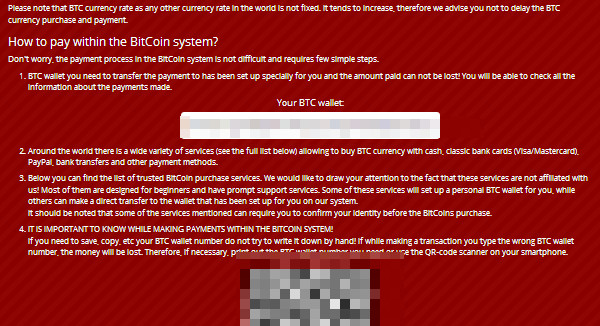
In the Payment tab, it displays the following for ransom Payment procedure:
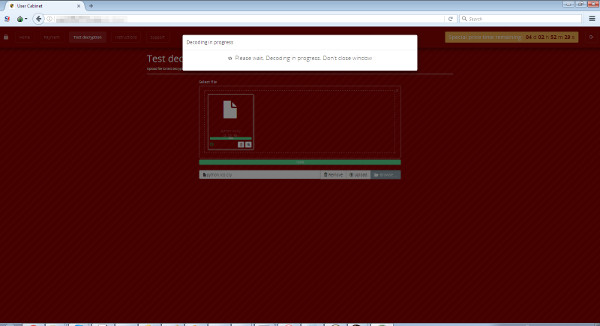
In the Test Decryption tab, it displays the following:
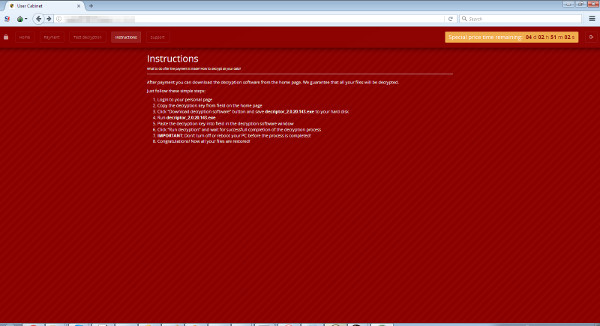
In the Instructions tab, it displays the following for decryption instructions:
And in the Support tab, it displays the following:
SOLUTION
Step 1
Before doing any scans, Windows XP, Windows Vista, and Windows 7 users must disable System Restore to allow full scanning of their computers.
Step 2
Note that not all files, folders, and registry keys and entries are installed on your computer during this malware's/spyware's/grayware's execution. This may be due to incomplete installation or other operating system conditions. If you do not find the same files/folders/registry information, please proceed to the next step.
Step 3
Delete this registry key
Important: Editing the Windows Registry incorrectly can lead to irreversible system malfunction. Please do this step only if you know how or you can ask assistance from your system administrator. Else, check this Microsoft article first before modifying your computer's registry.
- In HKEY_CURRENT_USER\Software\{random file name}
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\CtlGuid
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\CtlGuid
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\ServiceCtlGuid
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\WLanDiagCtlGuid
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\WLanDiagCtlGuid
- In HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\DiagL2SecCtlGuid
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\WDiagCoreCtlGuid
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Tracing\WDiagCoreCtlGuid
Step 4
Search and delete this file
- %User Startup%\{random file name 1}.lnk
- %User Startup%\{random file name 2}.lnk
- %User Temp%\{random file name 3}.html
- C:\0.tmp
- C:\1.tmp
- D:\2.tmp
- D:\3.tmp
Step 5
Scan your computer with your Trend Micro product to delete files detected as RANSOM_MILICRY.A. If the detected files have already been cleaned, deleted, or quarantined by your Trend Micro product, no further step is required. You may opt to simply delete the quarantined files. Please check this Knowledge Base page for more information.
Step 6
Restore encrypted files from backup.
Step 7
Search and delete these folders
- DATA_GENERIC
For Windows Vista, Windows 7, Windows Server 2008, Windows 8, Windows 8.1, and Windows Server 2012:
- Open a Windows Explorer window.
- For Windows Vista, 7, and Server 2008 users, click Start>Computer.
- For Windows 8, 8.1, and Server 2012 users, right-click on the lower left corner of the screen, then click File Explorer.
- In the Search Computer/This PC input box, type:
DATA_GENERIC - Once located, select the file then press SHIFT+DELETE to permanently delete the folder.
- Repeat steps 2-3 for the remaining folders:
- DATA_GENERIC
Did this description help? Tell us how we did.

